Reading time: 3 min
Table of Contents
Key Takeaways
- Real attacks, not drills: Poland detected compromises at five water plants — hackers could have altered chemical levels and disrupted supply. This is a production failure pattern, not a tabletop exercise.
- Unpatched PLCs are the entry point: Most industrial control systems run on outdated programmable logic controllers with default creds. That’s not security — that’s a liability.
- The cost is operational shutdown: Every incident costs time, trust, and regulatory exposure. The structural fix is automation with built-in monitoring and zero-trust access.
Water Treatment Vulnerabilities Exposed
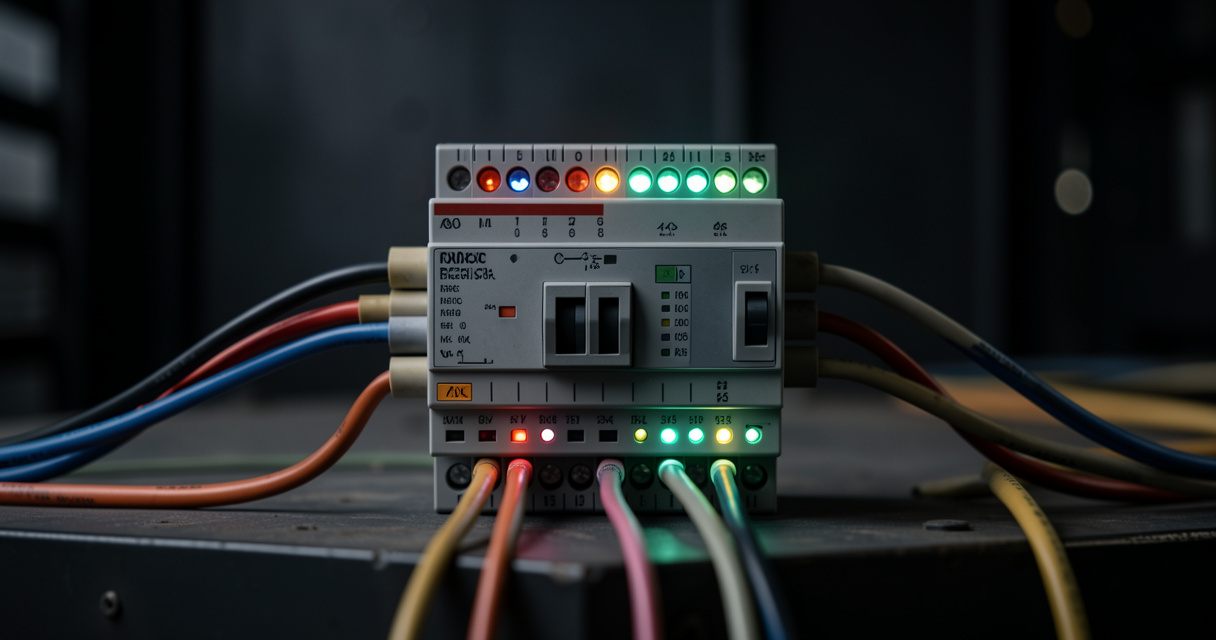
Here’s what actually happens in production: Poland’s Internal Security Agency confirmed they foiled sabotage attempts at five water treatment plants. Hackers had access to industrial controllers — the kind that manage chemical dosing, flow valves, and safety interlocks. In the worst-case scenario, an attacker could have tampered with water safety protocols. Most people get this wrong — they think it’s about fancy zero-days. It’s not. It’s about basic access control left wide open.
Poland Is a Warning, Not an Outlier
This isn’t theory. The same pattern hit Oldsmar, Florida in 2021 — a hacker briefly raised sodium hydroxide levels to dangerous concentrations. The FBI and CISA warned then that utilities are soft targets. Poland’s experience parallels that: state-backed actors, weak security hygiene, and industrial protocols that prioritize uptime over authentication. The real cost is not just remediation — it’s the downtime, the regulatory fines, and the erosion of public trust.
Why Automation Stacks Fail Under Attack
Let me be specific. Most water facilities run PLCs and SCADA systems that were designed 20 years ago for air-gapped environments. Now they’re connected to the internet with zero network segmentation. From a DevOps perspective, that’s like exposing your production database without a firewall. I’ve seen this in startups too — people build automation pipelines that work in a demo but collapse when a single default credential is changed. You need an architecture that assumes compromise and isolates blast radius.
The Structural Fix Isn’t Complicated
We built Hermes and OpenClaw to solve exactly this class of problem — not for demos, but for production environments where reliability is non-negotiable. The playbook is: apply zero-trust to every device, enforce least privilege on every API call, and monitor for anomalous behavior in real time. That’s not automation — that’s a strategy. For startups reading this, you don’t need to rebuild from scratch. Start with network segmentation and credential rotation. The incremental cost is far less than the cost of an incident.